One of life's minor annoyances is having to wait on my devices to connect to the network after I wake them from sleep. All too often, I'll open the lid on my EeePC netbook, enter a web address, and get the dreaded "This webpage is not available" message because the machine is still working on connecting to my Wi-Fi network. On some occasions, I have to twiddle my thumbs for as long as 10-15 seconds before the network is ready to be used. The frustrating thing is that I know it doesn't have to be this way. I know this because I have a Mac. When I open the lid of my MacBook Pro, it connects to the network nearly instantaneously. In fact, no matter how fast I am, the network comes up before I can even try to load a web page. My curiosity got the better of me, and I set out to investigate how Macs are able to connect to the network so quickly, and how the network connect time in other operating systems could be improved.
posted at 2011-07-12 02:23:17 MDT
by David Simmons
tags: mac dhcp networking
 An on-screen trackpad and keyboard allow a computer to be remote controlled.
An on-screen trackpad and keyboard allow a computer to be remote controlled.
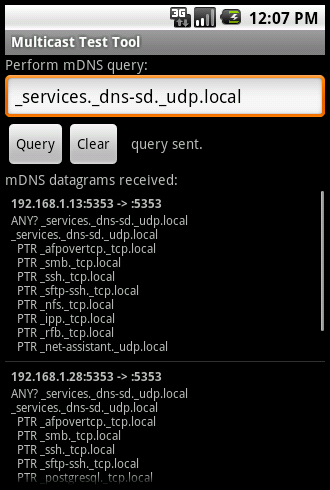
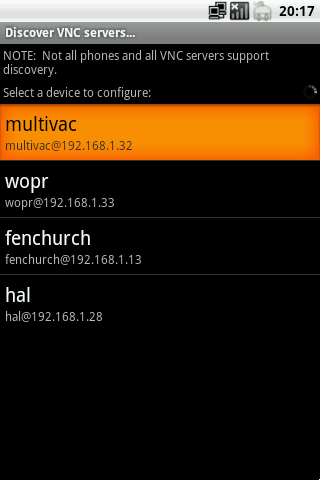 Valence supports mDNS service discovery (aka Bonjour or Avahi) to locate participating VNC servers on the local network.
Valence supports mDNS service discovery (aka Bonjour or Avahi) to locate participating VNC servers on the local network.