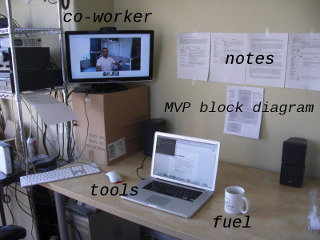
While finishing up my holiday travel, I decided to stop in for a couple of days at the Kansas City Hacker House, a place for aspiring technology entrepreneurs to live and work on their projects while connected to the Google Fiber gigabit network. Unlike my previous Google Fiber experience, I had an opportunity to plug my laptop directly into the network via gigabit ethernet and run some more tests.
Legacy Tests
I first ran a few tests of legacy network usage -- uploading and downloading large files from various services.
posted at 2012-12-28 23:24:39 MST
by David Simmons
tags: googlefiber kansascity hackerhouse